Repository secrets are used to store and manage sensitive information, such as passwords, tokens, and ssh keys. Storing this information in a secret is considered safer than storing it in your configuration file in plain text.
Push access or administrator access is required to create, update or delete repository secrets.
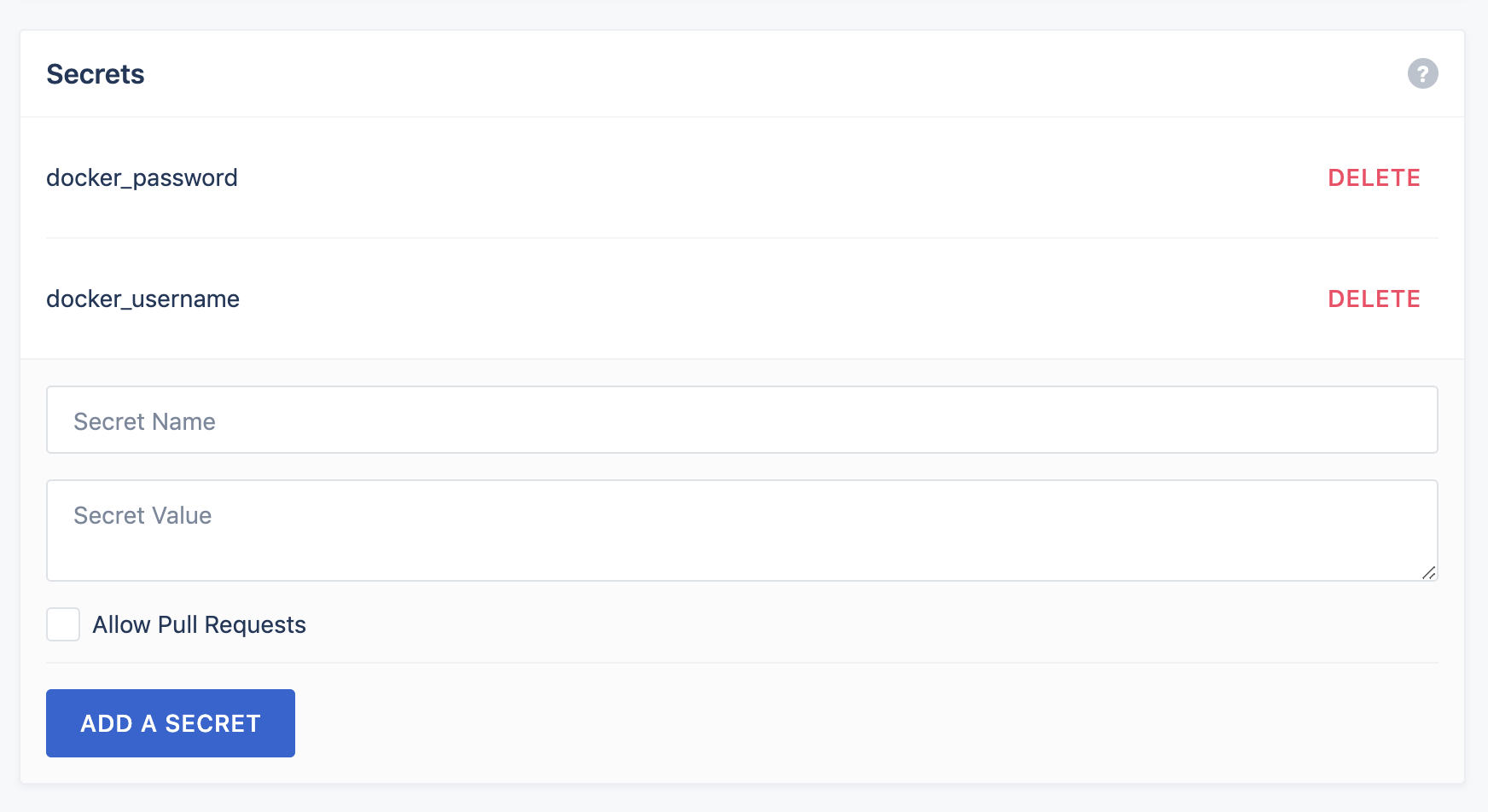
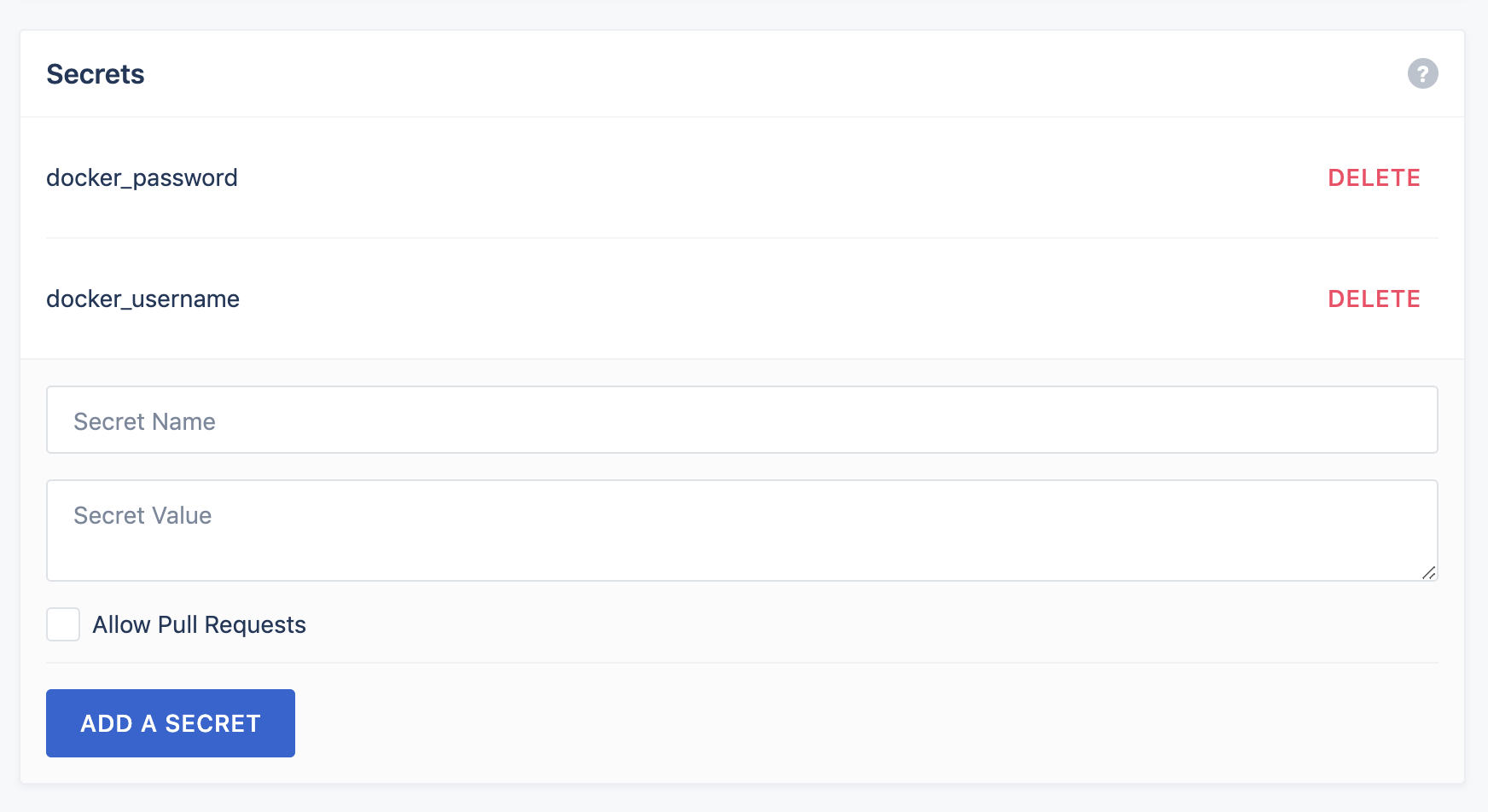
Manage repository secrets from the repository settings screen:
Source environment variables from named secrets:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
kind: pipeline
name: default
steps:
- name: build
image: alpine
environment:
USERNAME:
from_secret: docker_username
PASSWORD:
from_secret: docker_password
commands:
- echo "You can call the secrets like this examples below."
- echo $USERNAME
- echo $PASSWORD
- echo "In both cases, and for security reasons, you will see asteriks '*******' instead the value under the echo command."
|
Source plugin settings from named secrets:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
|
kind: pipeline
name: default
steps:
- name: build
image: plugins/docker
settings:
repo: octocat/hello-world
username:
from_secret: docker_username
password:
from_secret: docker_password
commands:
- echo "You can call the secrets like this examples below."
- echo $USERNAME
- echo $PASSWORD
- echo "In both cases, and for security reasons, you will see asteriks '*******' instead the value under the echo command."
|
Pull Requests
Secrets are not exposed to pull requests by default. This prevents a bad actor from sending a pull request and attempting to expose your secrets. You can override this default behavior, at your own risk, by checking Allow Pull Requests when you create your secret.